Android Ransomware Can Change Your Mobile's PIN Code
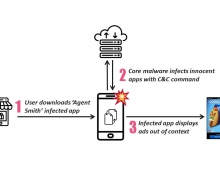
Researchers at security company ESET have idenified an Android lock-screen-type ransomware spreading in the wild that sets the phone’s PIN lock. In previous Android LockScreen Trojans, the screen-locking functionality was usually achieved by constantly bringing the ransom window to the foreground in an infinite loop. While various self-defense mechanisms were implemented to keep the device user locked out, it wasn’t too difficult to get rid of the malware thus unlocking the device by using Android Debug Bridge (ADB) or deactivating Administrator rights and uninstalling the malicious application in Safe Mode.
It seems that malware writers have stepped up their game, and with the new Android ransom-lockers, detected by ESET as Android/Lockerpin.A, users have no effective way of regaining access to their device without root privileges or without some other form of security management solution installed, apart from a factory reset that would also delete all their data.
Moreover, this ransomware also uses a trick to obtain and preserve Device Administrator privileges so as to prevent uninstallation. T
After it's installed, users see a warning supposedly from the FBI that they've allegedly viewed "prohibited pornography." It asks for a US$500 fine to be paid within three days.
The malware is also coded to try to shut down three mobile antivirus products: Dr. Web, ESET's Mobile Security and Avast.
More advanced users may be able to get rid of Porn Droid without resetting and erasing all data on their phone. It is possible to remove the malware if a user has root privileges to the device, and some security software can stop it, the researcher said.
Ransomware attacks, both desktop and mobile, have become some of the most persistent and damaging scams on the Internet. One of the most prevalent scams is encrypting a person's files and asking for money for the files to be decrypted.
Security experts generally advise not paying the ransom, as in many cases fraudsters never bother to fix the victim's computer.