Android Devices Vulnerable To Physical RAM Attack
Attackers can flip bits in the physical memory cells of Android devices in order to compromise them, researchers proved.
Researchers at the VUSec Group at Vrije Universiteit Amsterdam in the Netherlands, the Graz University of Technology in Austria, and the University of California in Santa Barbara has demonstrated how a weakness of the physical design of RAM chips can be used in order to attack
ARM and x86-based hardware.
The attack stems from the push over the past decade to pack more DRAM (dynamic random-access memory) capacity onto increasingly smaller chips, which can lead to memory cells on adjacent rows leaking electric charges to one another under certain conditions.
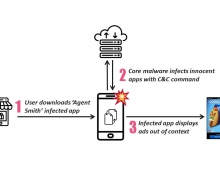
The hardware bug DRAM (dynamic random-access memory) allows attackers to manipulate data in memory without accessing it. More specifically, by reading many times from a specific memory location, somewhere else in memory a bit may flip (a one becomes a zero, or a zero becomes a one).
The technique hsa been identified by researchers from Google's Project Zero last year. It is based on the the memory "row hammer" effect on the x86-64 CPU architecture. One of the exploits allowed code to escape the Google Chrome sandbox and be executed directly on the OS and the other gained kernel-level privileges on a Linux machine.
The latest research proves that Rowhammer is possible on mobile, ARM-based hardware. The researchers dubbed their new attack Drammer, which stands for deterministic Rowhammer, and plan to present it Wednesday at the 23rd ACM Conference on Computer and Communications Security in Vienna.
The VUSec researchers developed an Android app - not yet in Google Play, but available directly - to test mobile devices for the Rowhammer bug. The app uses a native binary for which the researchers also released the source code. After a successful run, the app uploads anonymized output.
The researchers tested 27 Android devices from different manufacturers, 21 using ARMv7 (32-bit) and six using ARMv8 (64-bit) architectures. They managed to flip bits on 17 of the ARMv7 devices and one of the ARMv8 devices, indicating they are vulnerable to the attack.
Among the vulnerable devices listed are the LG Nexus 4 and Nexus 5 , the Motorola Moto G (2013) and Motorola Moto G (2014), the OnePlus One, Samsung Galaxy S4 and the
Samsung Galaxy S5.
Google is aware of this type of attack and developed a mitigation which will be include in the upcoming November security bulletin.
Drammer was demonstrated on ARM-based devices running Android, but the underlying technique likely applies to all architectures and operating systems.