Twitter Disclosed Users' Phone Data Breach
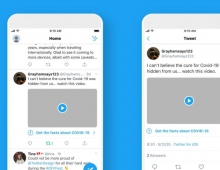
Twitter discovered attempts by possible state actors to access the phone numbers associated with user accounts, after a security researcher unearthed a flaw in the company’s “contacts upload” feature.
On December 24, 2019 Twitter said it became aware that someone was using a large network of fake accounts to exploit our API and match usernames to phone numbers. The company says it immediately suspended these accounts.
A company spokeswoman declined to say how many user phone numbers had been exposed, saying Twitter was unable to identify all of the accounts that may have been impacted.
She said Twitter suspected a possible connection to state-backed actors because the attackers in Iran appeared to have had unrestricted access to Twitter, even though the network is banned there.
During an investigation, Twitter discovered additional accounts that the company believes may have been exploiting this same API endpoint beyond its intended use case. While Twitter identified accounts located in a wide range of countries engaging in these behaviors,the company observed a particularly high volume of requests coming from individual IP addresses located within Iran, Israel, and Malaysia. "It is possible that some of these IP addresses may have ties to state-sponsored actors," Twitter said.
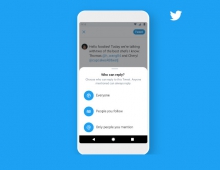
When used as intended, this endpoint makes it easier for new account holders to find people they may already know on Twitter. The endpoint matches phone numbers to Twitter accounts for those people who have enabled the “Let people who have your phone number find you on Twitter” option and who have a phone number associated with their Twitter account. People who did not have this setting enabled or do not have a phone number associated with their account were not exposed by this vulnerability.
Twitter says it made a number of changes to this endpoint so that it could no longer return specific account names in response to queries. Additionally, the company suspended any account we believe to have been exploiting this endpoint.